ASN.1 Viewer 
An option to display ASN.1 data structures, support for DER, PEM, PKCS#7, and PKCS#12 file formats, and manual input in hex and base64 formats. Includes support for common x.509 field types. See ASN.1 Viewer
DirSync 
An option to run an LDAP query with the DirSync server side control to display what changes have been made in the select context. See DirSync
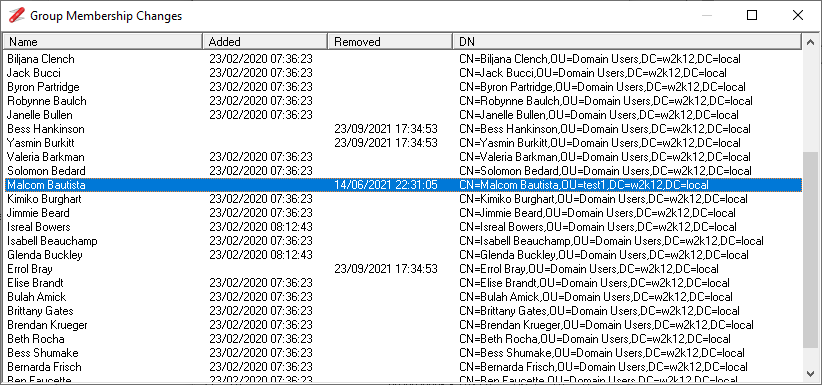
Domain Changes 
An option to display which objects have been changed/created or replicated to the domain controller, based on the objects with updated USNChanged attribute. See Domain Changes
Object Counts 
An option to count the number of different types of objects that exist under the selected OU structure. Selectable object types for Users, Groups, Computers, Active Users, OU and all objects. See Object Counts
User's Membership 
An option to display a user's group membership, including nested groups and which group contributed to the user's groups. See User's Membership
General
Updated the icons and context menu icons.
Added additional command line options to allow a LDAP Search Favorite to specified and run from the command line, /f:<favorite name>, i.e. NetTools "/f:AD: RootDSE" The /Q option is also available which will cause NetTools to quit after the query has finished running.
Added a new Find feature to enable searching for items in the result.
Added Open Container context menu to open the parent container in LDAP Browser.
Added LDIF Export option to context menus to allow the objects to exported to file in ldif file format.
Time and Dates now displayed based on locale and regional settings, LDAP Search Substitution input entries also use locale date format for entry.
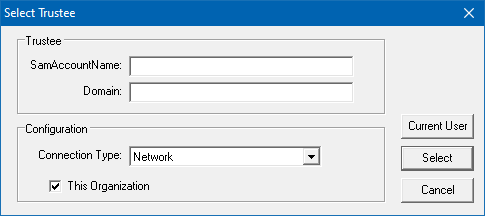
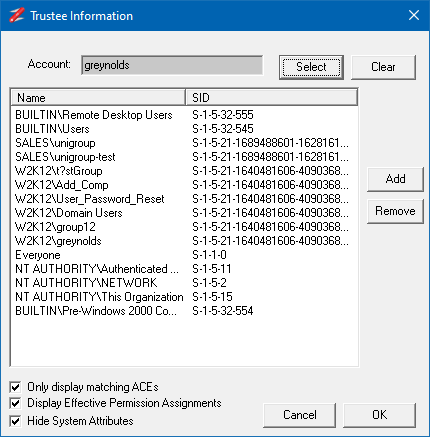
Options that require a username (SamAccountName) entry, now display a user search dialog if the entered name is not found.
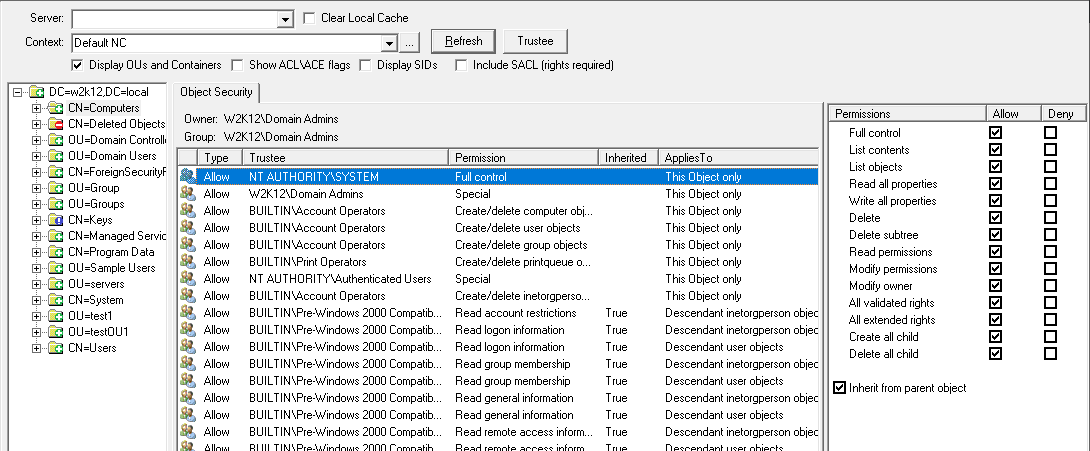
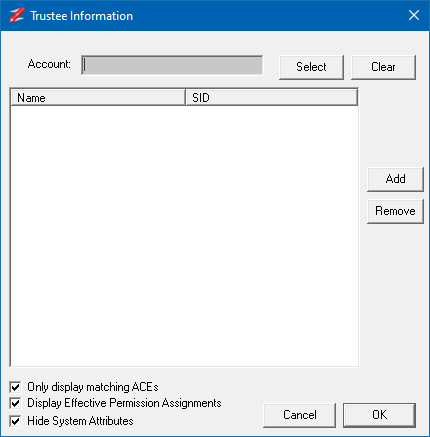
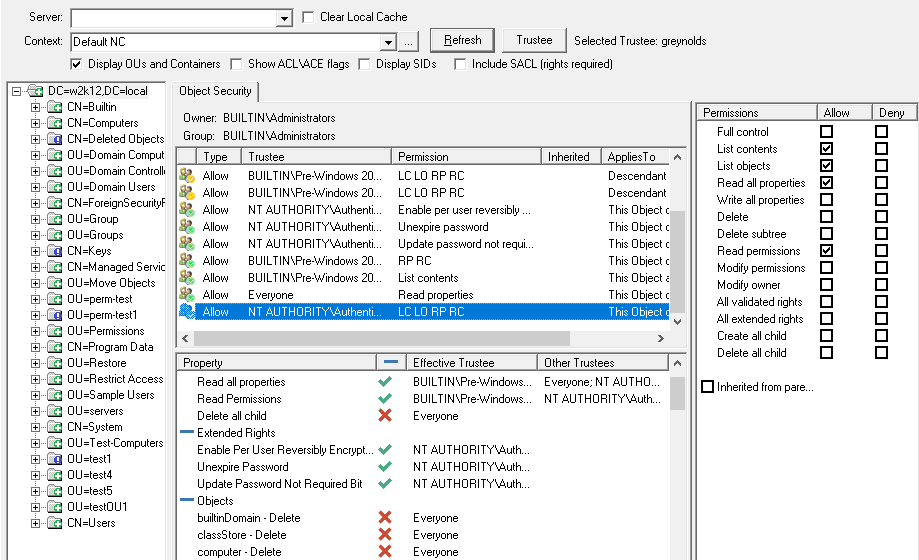
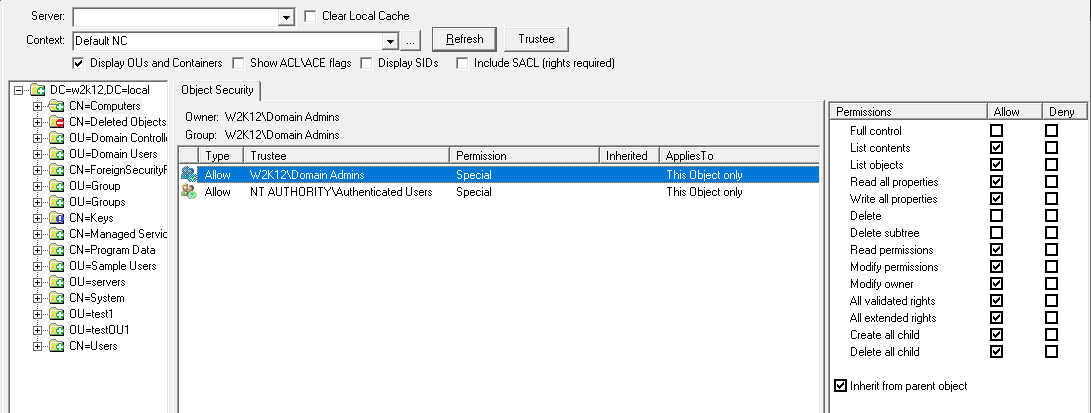
ACL Browser
Added Group Members and Group Manager options to the context menus.
Fixed intermittent exception error when copying multiple items.
Fixed display issue associated to member attribute and add\remove self to group extended right.
AD Attributes
Updated to remove the dependency on the AllowedAttributes to allow the objects from non AD based directories to be displayed.
AD Properties
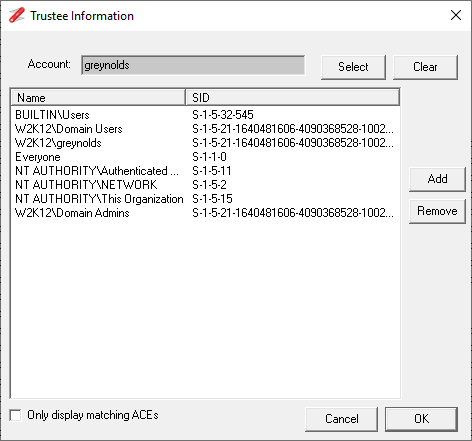
Updated the TokenGroups tab to include the SID of the names that are resolved against each entry. Also includes an option to use Absolute SID Resolution, this is to help identify any entries that are associated to SID History.
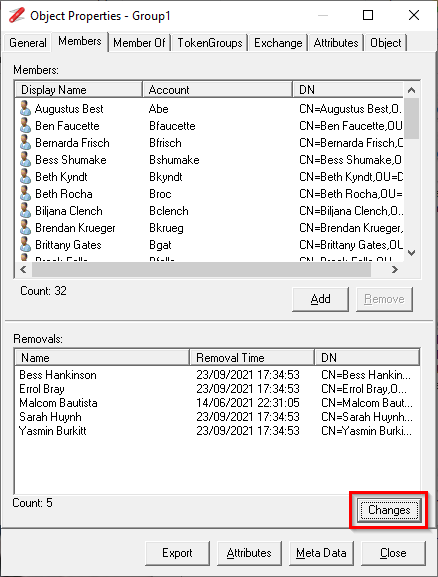
Updated Members tab to also display which members have been removed from the group and when.
Updated the object selector used to manage group membership to support a paste option, so multiple entries can be added to the selection list. Supports DN, samaccountname, upn, email, and name, with any combination of these.
Added option on Logon tab to perform a Last Logon scan.
Added option to display organisation structure from Organisation Tab.
Updated the Members and MemberOf lists to include the samaccountnames of included objects
Base64
Updated to use dynamic buffers rather than static to allow for larger decodes.
Added option to decode output to file.
Added option to be able to display hex or base64 outputs in the ASN.1 viewer.
Improved the handling of the extra space in the data input.
Updated to support Hex stream data input format.
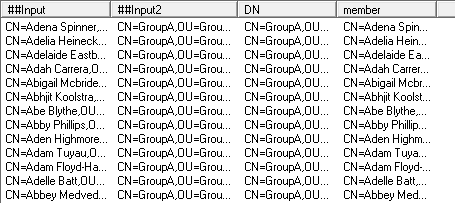
Compare Groups
Updated so it can compare both member and memberof attributes, so it can be used to compare the membership of groups as well as users.
Copy To Windows
Improved the performance when displaying large list of items and better indication to the user when the program is busy.
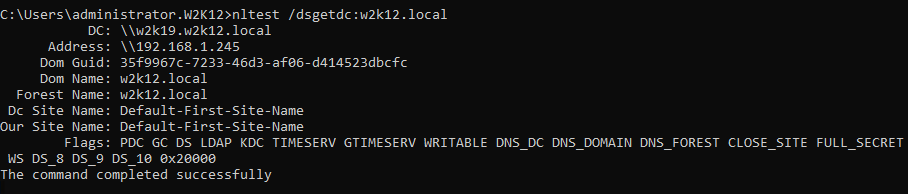
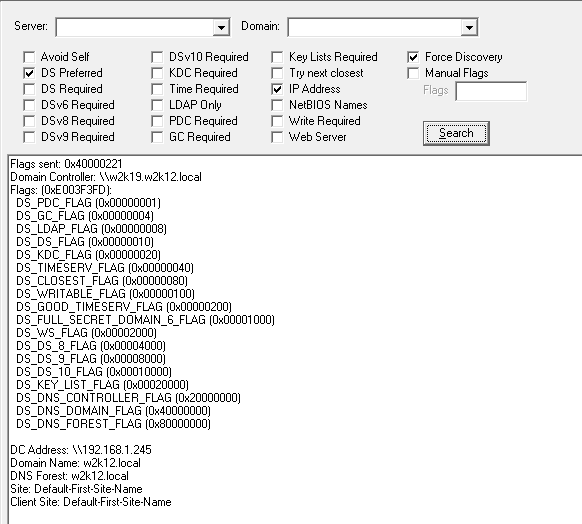
DsGetDcName
Updated the selectable options to include DS8, DS9, DS10, and Key Lists.
Updated the flags decode to display the full flags names, and added support for DS9, DS10, Key Lists.
DC Resolution
Updated the ports option to allow lists of ports to be defined and selected, simplifying the testing of different services.
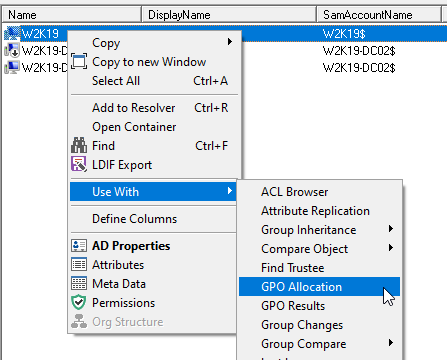
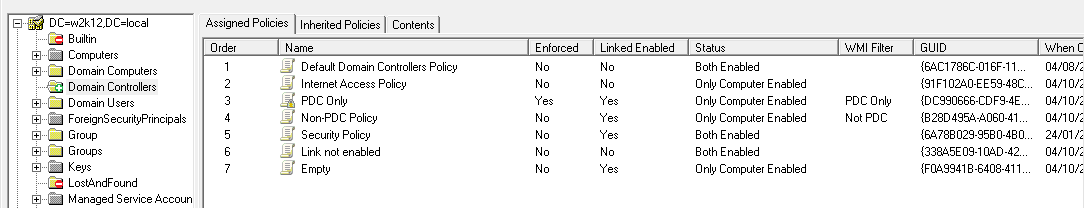
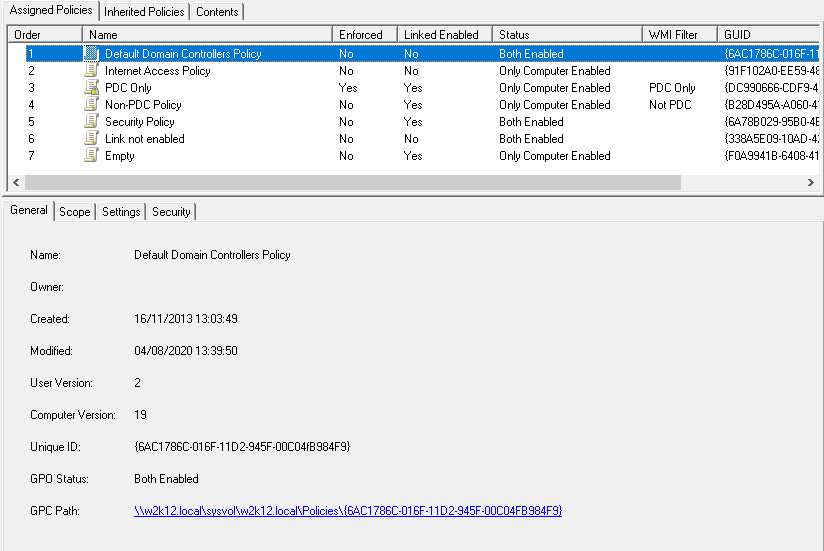
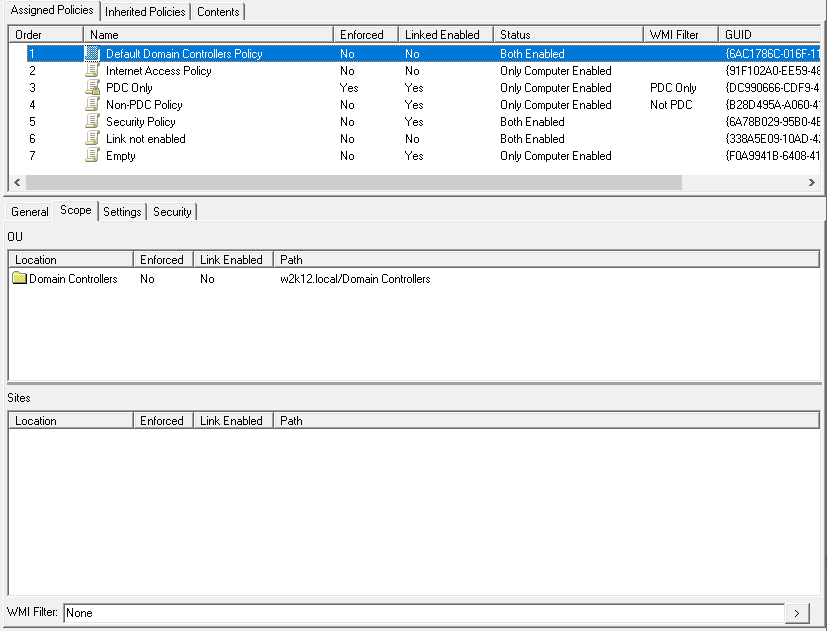
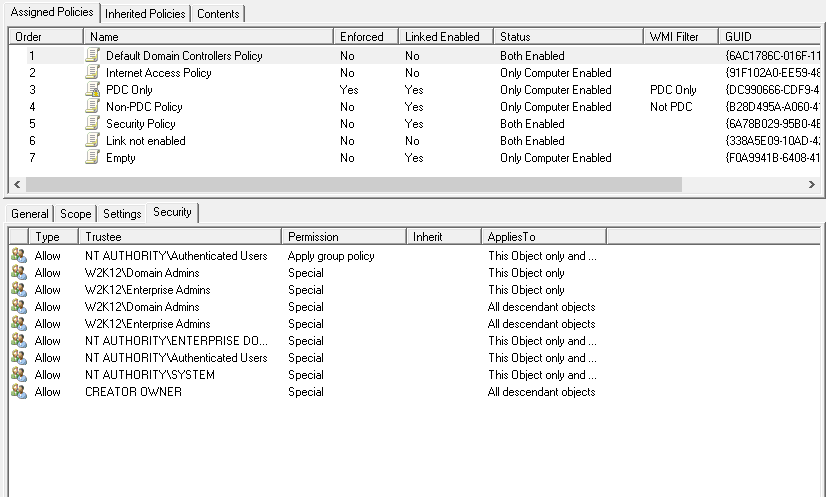
GPO Explorer
Added AD Sites view with indication if policies are applied to a site.
Double click to WMI filter viewer to display policy details.
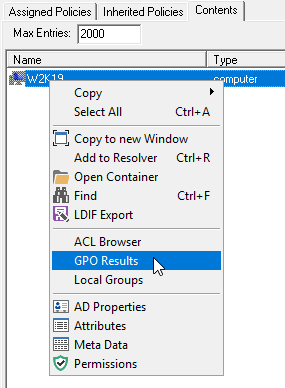
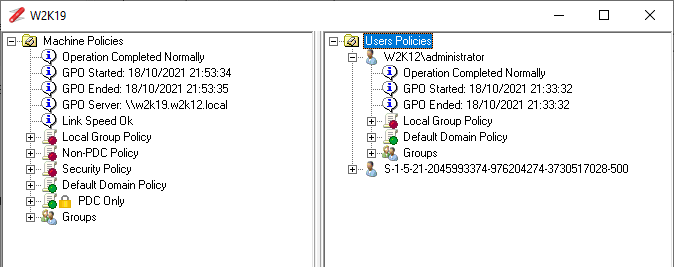
Added GPO Results to context menu to the Content tab of the GPO Allocation view to display which policies have been applied to a selected machines.
Updated to display the wireless and wired GPO settings.
Updated to display which client side extensions are assigned to the GPO.
Updated the Settings view for the registry items to display all the registry entries in the registry.pol as a single list, the option is available by clicking on the Settings item at the top of the registry tree.
Updated a number of context menus to include some of the standard options, which were missing.
Updated GPO List view to include the split screen option to display the selected GPO properties below the list.
Added context menu item to display all OUs that have block Inheritance enabled.
Added additional error handle to GPO that don't have the display name set or gplink attributes with invalid format
Last Logon Time
Added accumulative logon Count across all domain controllers and DN
Added context menu option to input a new entry
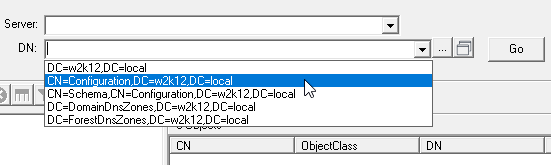
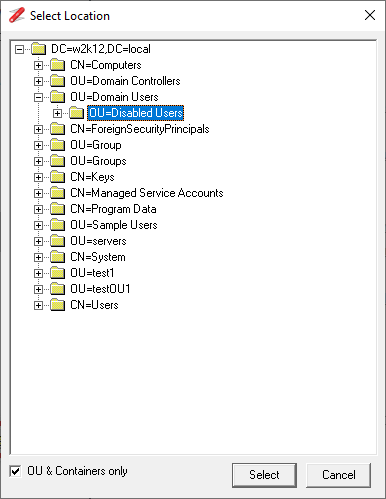
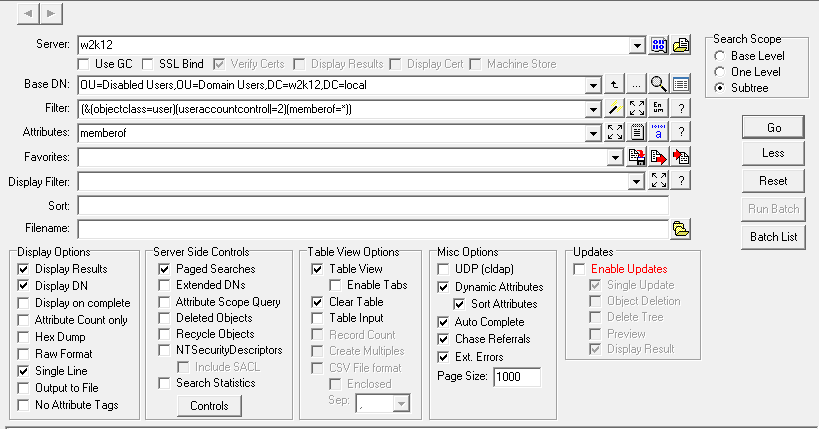
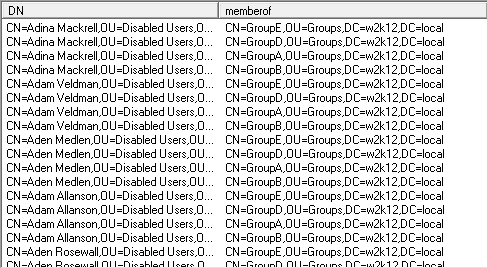
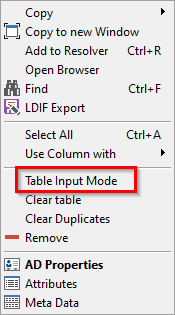
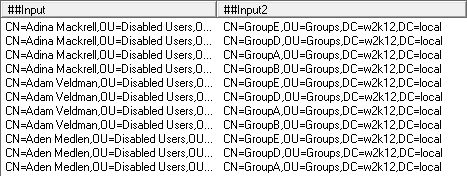
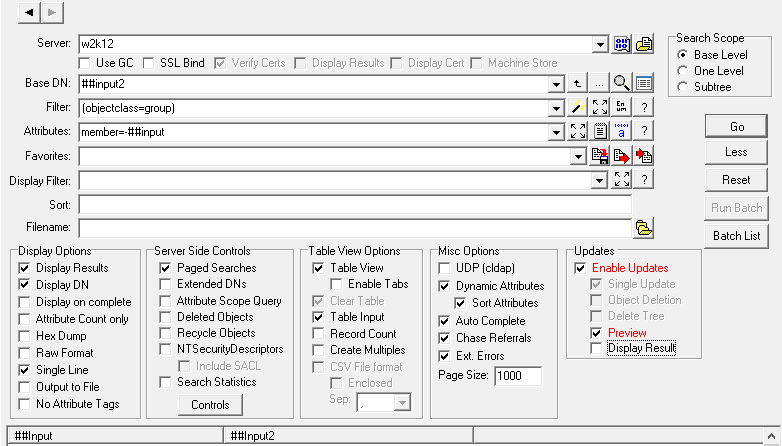
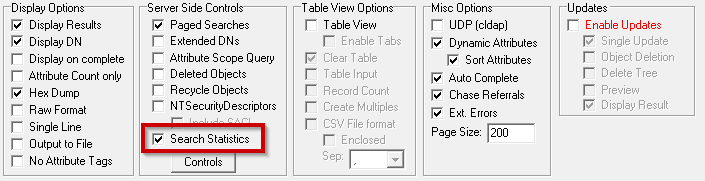
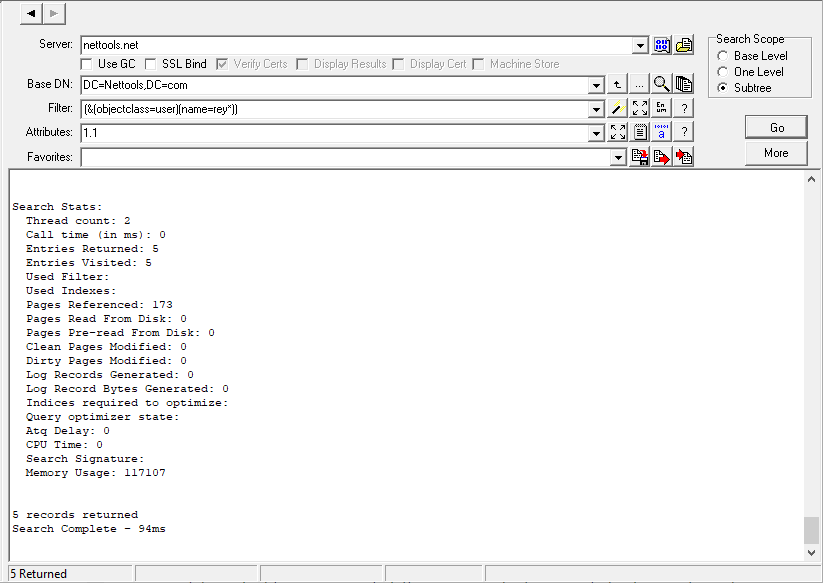
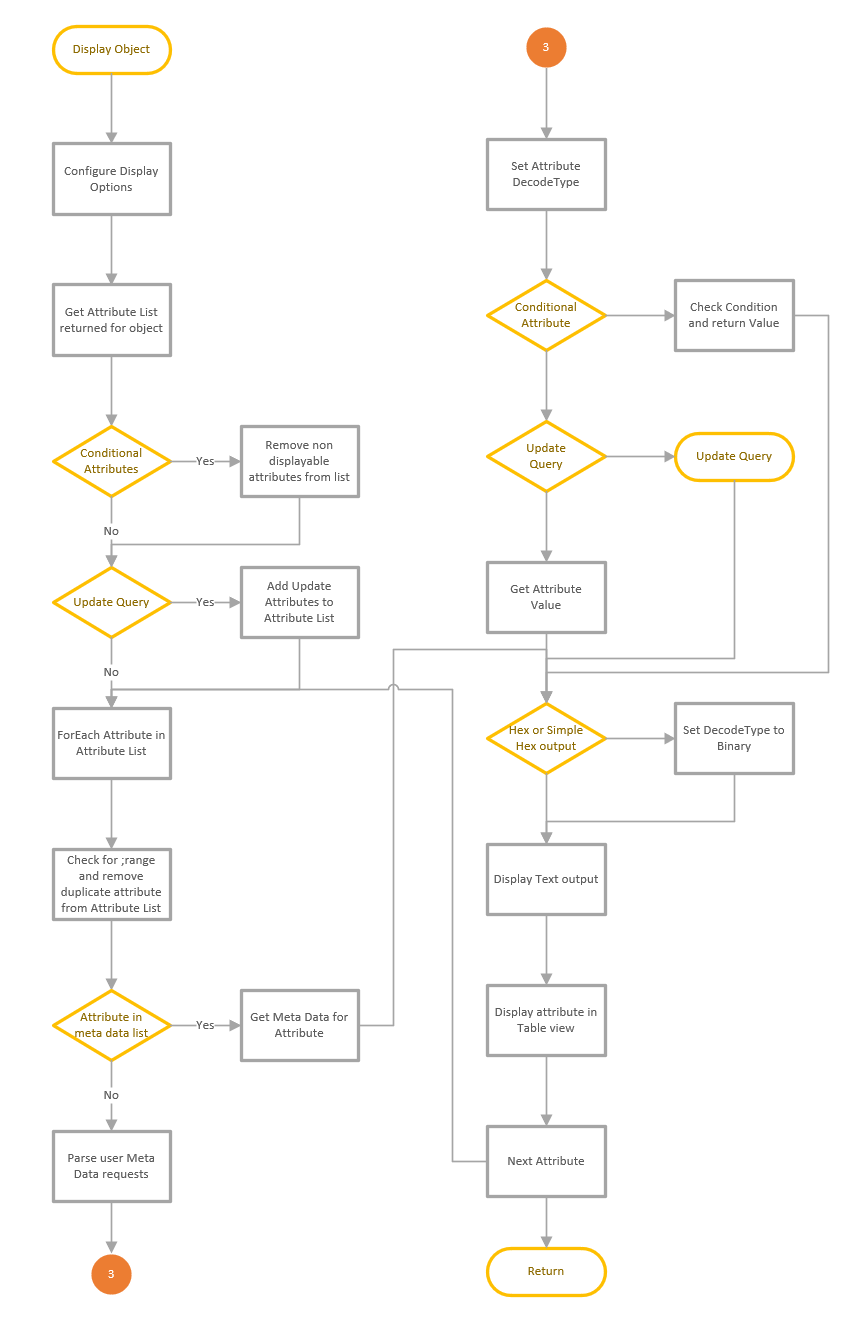
LDAP Search
Conditional Attributes - updated logic so an attribute with no value set is also tested against the condition statement. i.e. location!=london will be true if no value is set.
Conditional Attributes - updated so the position of the wildcard character is position sensitive, if the wildcard character is placed at the begin of the search criteria i.e. *disable, then 'disable' will match any where in the attribute. If the wildcard is placed at the end of the search citeria i.e. disable*, the a match only occurs if disable is at the start of the attribute.
Conditional Attributes - the entered case of static entries is now persevered.
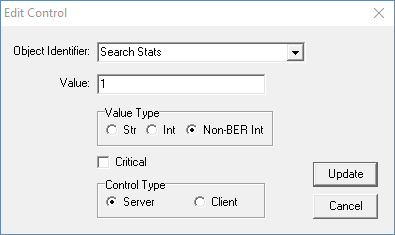
Custom Controls updated to allow data encoding type to be defined, data can now be defined as String or Integer encoded using BER encoding, or Non-BER encoded Integer.
Option to display server controls that are sent and returned as a hex dump and ASN.1 structure dump in the text output view, option is selected in the Manage Controls dialog.
Updated Search Statistics option to automatically change which sets of search stats are returned based on the domain controller functional level.
Updated Attributes field to also support the getdn substitution, so they can be used in the update queries.
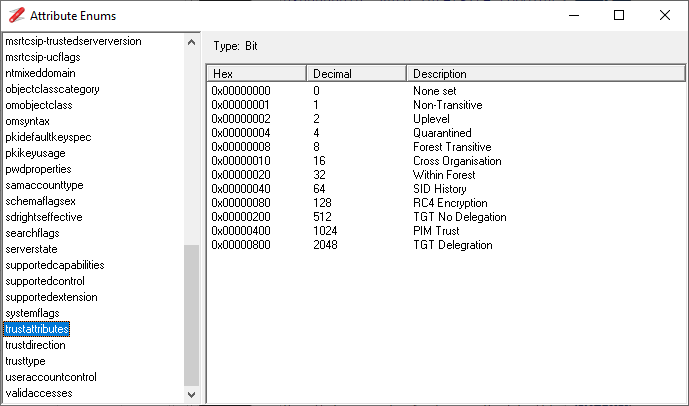
Updated the MSTRUST DecodeType for the msds-TrustForestTrustInfo attribute to provide details of excluded routing suffixes.
Updated Filter processing to remove the case sensitivity of boolean expressions.
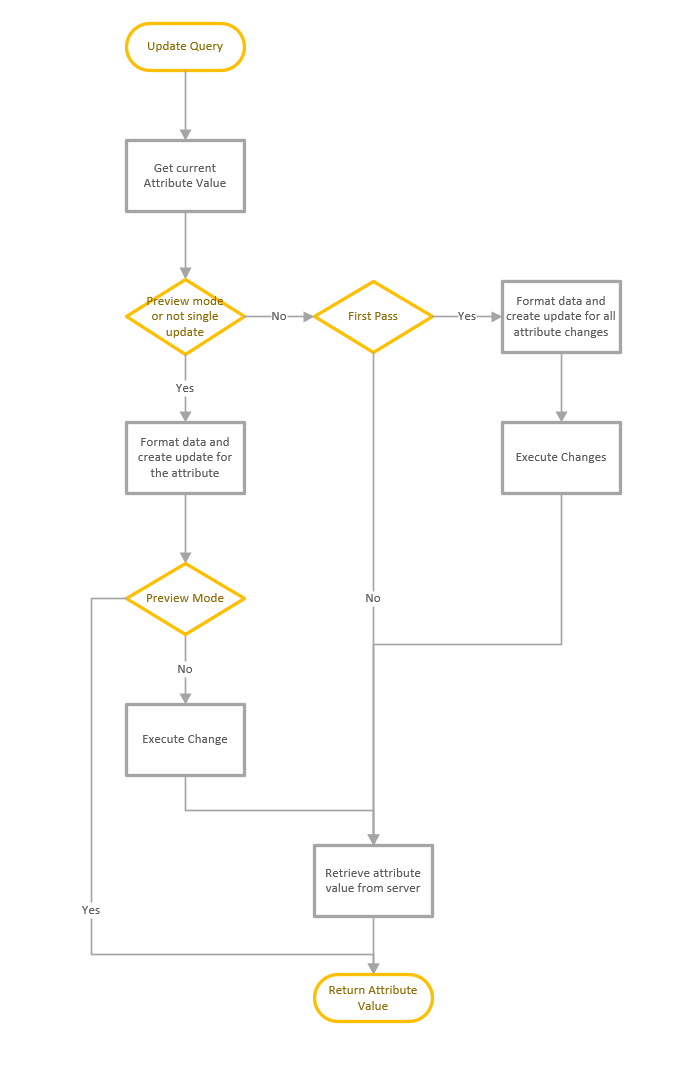
When the Display Results option is not selected with Update Queues, it will prevent the attribute pre-read before updates which significantly improves the performance when updating attributes with more than a few thousand values.
Updated REPS_INFO DecodeType, used by repsto and repsfrom attributes, to support V2 data structure format.
Updated file output logic, so when file output is selected and Display Results is not selected, the results are written to the file. Fixed bug with single line option so all entries are now written to the file. Fixed bug with tab separated character.
Updated Use column with context menu to include add to Resolver.
Added new GPLINKS DecodeType to return a list of GPO DNs in the gplink attribute
Added a shift key function to disable html parser when pasting items in Input Mode.
Added new METAP DecodeType, used for the replPropertyMetaData attribute.
LDAP Search - Predefined Queries
The following predefined queries have been added:
AD: Schema Attributes ANR Indexed
AD: Schema Attributes Confidential
AD: Schema Attributes Constructed
AD: Schema Attributes in GC
AD: Schema Attributes Indexed
AD: Schema Attributes Not Replicated
AD: Schema Attributes Tuple Indexed
The following predefined queries have been updated:
GPOs: All
GPOs: All deleted
GPOs: Computer Targeted Policies
GPOs: Created in Last 30 Days
GPOs: Created in Last 60 Days
GPOs: Created in Last 7 Days
GPOs: Created in Last 90 Days
GPOs: Created Today
GPOs: Created Yesterday
GPOs: Deleted in the last 24 hours
GPOs: Deleted in the last 48 hours
GPOs: Modified in Last 30 Days
GPOs: Modified in Last 60 Days
GPOs: Modified in Last 7 Days
GPOs: Modified in Last 90 Days
GPOs: Modified Today
GPOs: Modified Yesterday
GPOs: Non Active
GPOs: Policies with a WMI Filter
GPOs: User & Computer Targeted Policies
GPOs: User Targeted Policies
GPOs: WMI Filters
Groups: All
SCCM: Management Points
SCCM: Site Boundaries
SCCM: Sites
Users: Active Users Who Haven't Logged On In Last x Days - user defined period
Users: Without Home Directory
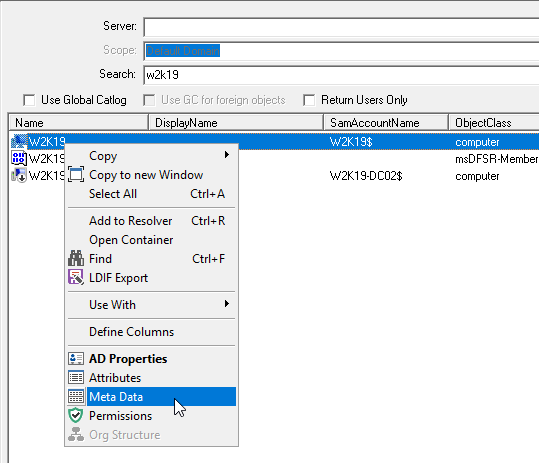
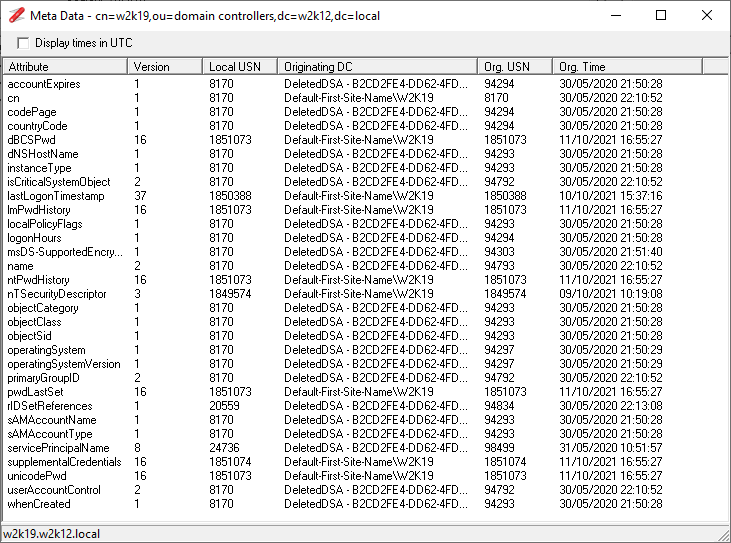
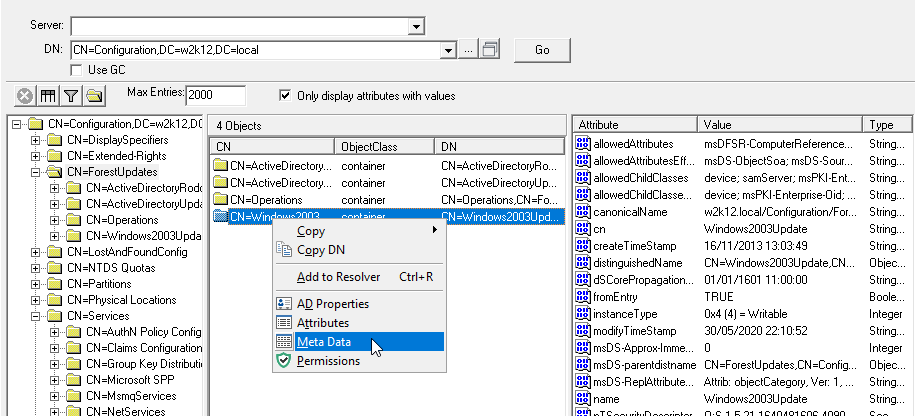
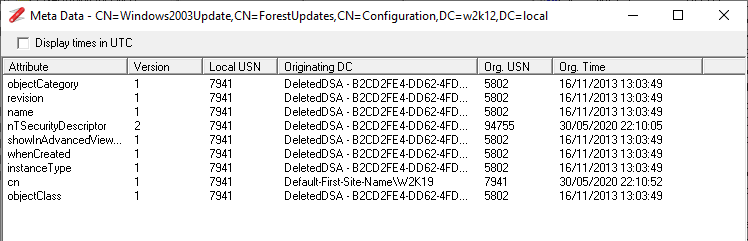
Meta Data Dialog
Updated Value replication table to include local and originating USN details.
NetGroupEnum
Renamed the option to Local Groups.
Organisation Structure
Change the default view to display reporting lines, including peers and direct reports as separate items. Still has the option to display the old tree view as this is more useful in some scenario.
Replication Queues
Updated authentication to use DSBindWithCred instead to DsBind to allow the credentials from the Connection Profiles to be used.
Resolver
Included a key shortcut to allow new entries to be manually entered using the Insert key.
Context menu updated to be object sensitive and will enable and disable options based on the object selected.
Display GPO Results added to the Use with context menu.
Fixed bug where the item count may be incorrect.
Updated to allow tracking of objects that have been opened or used with context menus
Added Object History option, so all object opened or linked via context menus are automatically added to the the Resolver list
Updated so each new entry added also records the server name.
SID Converter
Updated output view to use a table view to simplify the output and easier to copy details between options.
Added the option to display SID details from a Base64 format input.
Fixed bug where comma separated SIDs were not resolved correctly.
Schema Versions
Updated to include support for Exchange 2019 CU8, CU9 &CU10, 2016 CU19, 20 & CU21
Schema History
Updated with details of SCCM, Mapi Lab, EMC schema extensions
Updated to display Unknown if the schema extension is not in the internal database.
Time Converter
Updated to display the time outputs in a table view.
The time and date input are now based on the locale time\date format. The locale time\date format is displayed as the supported formats section.
Token Size
Updated the size column to reflect the Token Size based on the MS algorithm to calculate Token Size.
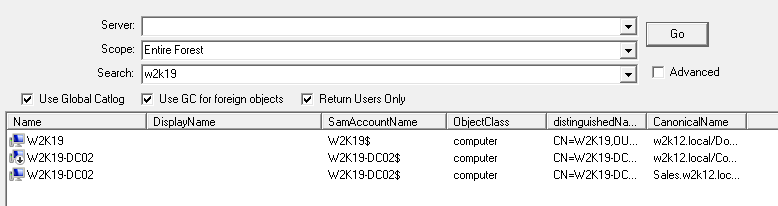
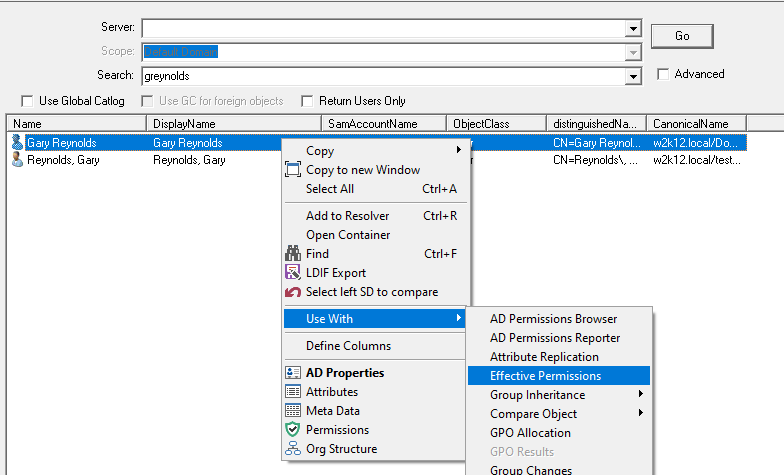
User Search
Updated Use With context menu to include Local Groups option, to allow the local groups of member machines to be viewed.
Updated Use With context menu to include GPO Results on computer objects that are returned.
Updated icons so there is a separate icon for expired users
Updated to include an advanced option to allow searching of specific attributes on nominated object.