Some of the feature shown are only in NetTools v1.31.5 and above
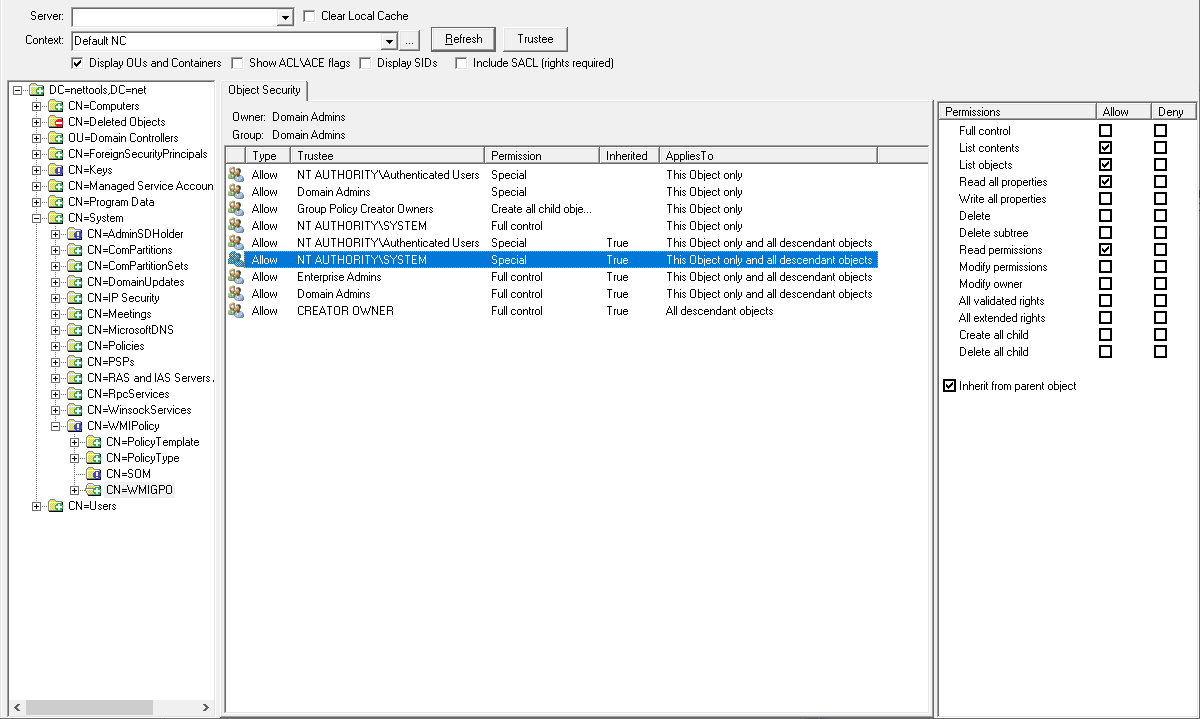
AD Permissions Browser provides a fast and simple method of browse the permissions that are assigned to objects in the directory. Unlike the standard AD security\permissions dialog, the option allows you to browser the OU structure, and quickly and easily display the permissions that have been assigned to objects in the AD. The option also provides the ability to view the effective permissions on AD objects for a selected user.
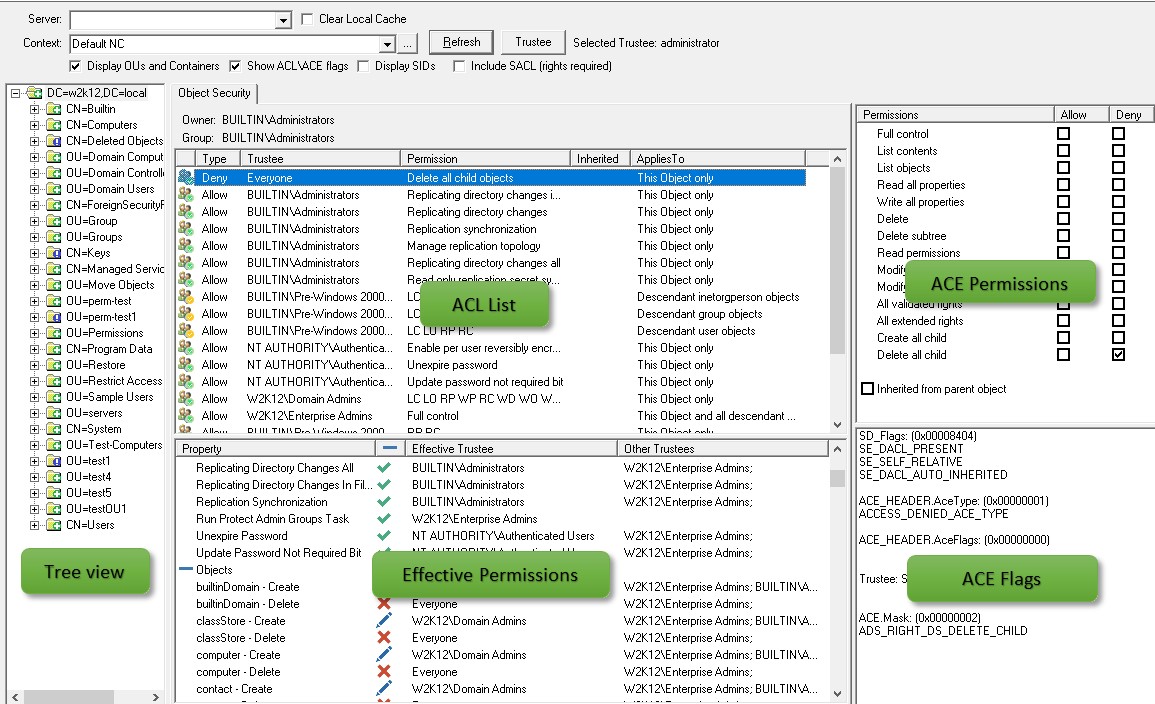
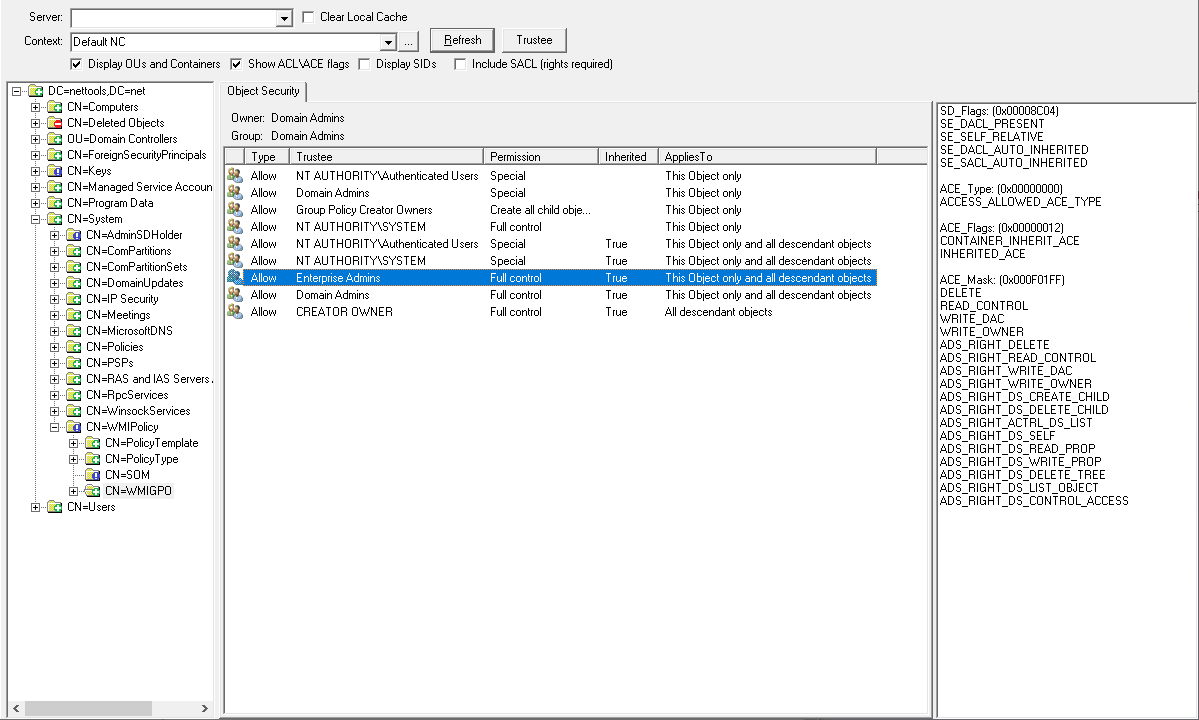
The AD Permissions Browser uses a familiar user interface layout as the standard AD management tools. The screen is split into three sections:
Tree View - This section provides the method to navigate the directory, clicking on an items in this pane will display the assigned permissions to that item. The Display OU and Containers options limits the displayed items to just these items, by deselecting this option the browser pane will display all the objects in the OU and containers.
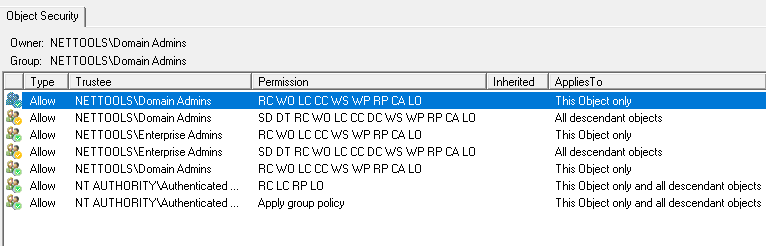
ACE List - This pane lists the ACEs that have been assigned to the selected items, by default the Object Security tab is displayed showing the Discretionary Access Control List (DACL). Depending on the item selected, the SACL, Mailbox, and Schema permissions will also be displayed. For SACL to be displayed the Include SACL option must be selected, for these to be displayed Domain Admin rights are required. If the Display SIDs option is selected an extra column is displayed with the SID of the trustee.
The Permissions field provides a brief description of the permissions that are assigned, for the permissions that would appear as special in the standard AD permissions dialog, NetTools will display the dsacls pneumonic/abbrevaitions for the permissions that have been assigned. The following list provides the details of the abbreviations that are shown in the Permissions field:
LC - List Contents
LO - List Object
RP - Read Properties
WP - Write Properties
SD - Delete
DT - Delete Subtree
RC - Read Permissions
WD - Write Permissions
WO - Write Owner
WS - Write Self - Validated Rights
CA - Control Access right - Extended Rights
CC - Create Child
DC - Delete Child
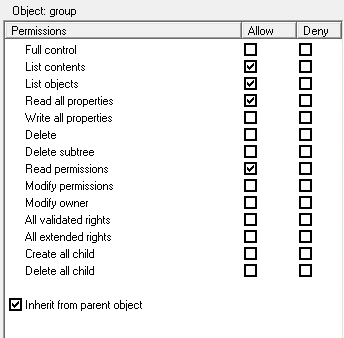
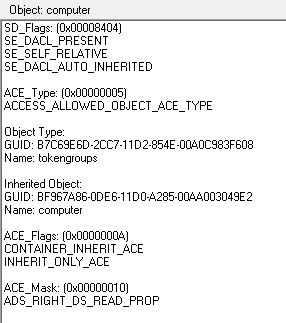
ACE - This pane displays the Access Control Entry based on the item selected in the ACE List pane. The list of permissions is dynamic based on the item selected, but the standard full/read/write/create/delete permissions are displayed for all items. When the Show ACL\ACE flags options is selected the ACE view will display the raw ACL and ACE flags associated to the selected item in the ACE List pane. The details of the flags that are displayed can be found here. When an Object Specific ACE is selected the name of the object type which the permissions are associated to is displayed above the ACE pane. In the example below the object type is User.
Here is the flags view, it showing the flag details based on the definition in the Windows Data Types. or AD Permissions - Advanced Filter Constants. If there is a flag value that is not recognized, then the underlying value will also be displayed.
Clear Local Cache - AD Permissions Browser uses a local cache for extended permission GUIDs and SIDs. As the results are retrieved from the server they are cached to improve the performance when viewing permissions. When changing to a new location and is Refresh pressed, if the forest\domain is the same then the cache is maintained, if the forest\domain has changed, the cache is purged, the cache will also be cleared if the Clear Local Cache option is selected. This cache is shared with the GPO Explorer security tab.
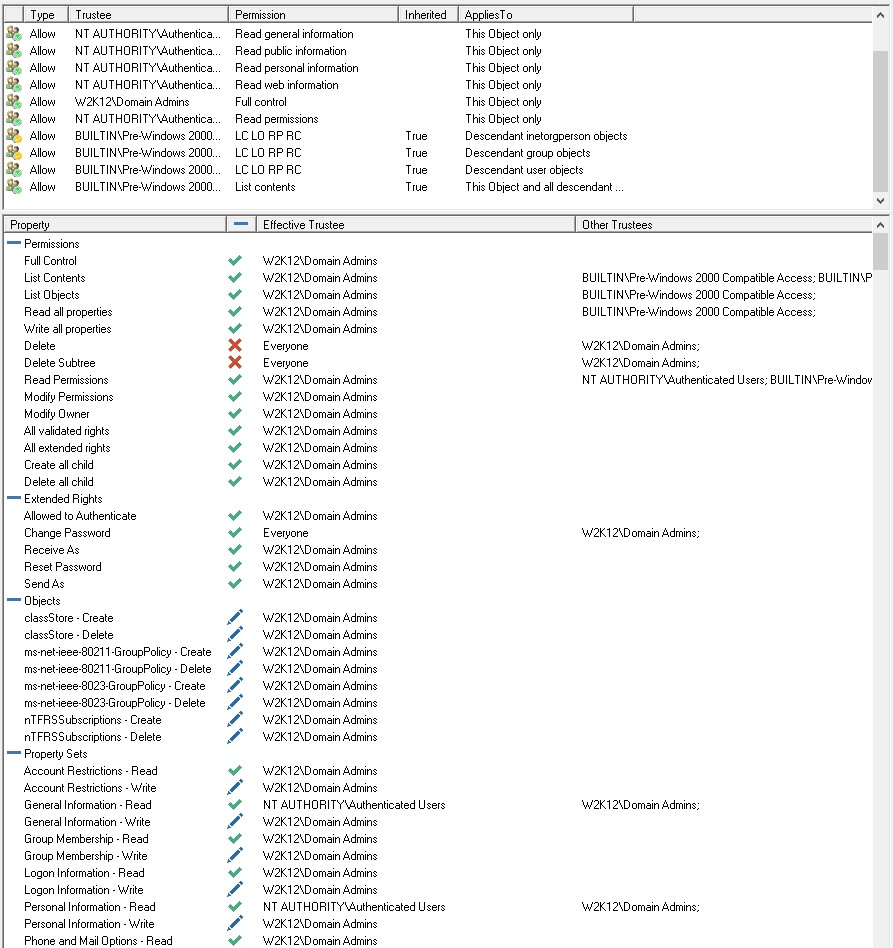
Trustee Mode - AD Permissions Browser has a Trustee mode, which allows a trustee (user, group, computer etc.) to be selected and then the ACE that apply to the trustee to be displayed and if selected the effective permissions will also be displayed. The icons in the ACE List pane will have a green tick to indicate that the corresponding ACE applies to the selected trustee. These are the effective rights for the selected trustee. ACE can also have an orange tick, while these ACE apply to the selected trustee, they are not applied directly to the selected object. Typically these are permissions that will inherited by descendant objects.
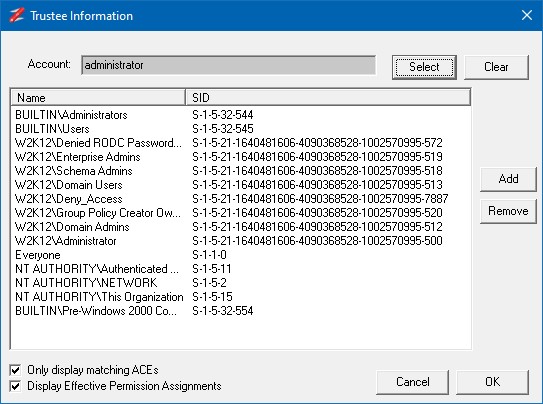
To Select the Trustee click on the Trustee button and the Trustee Information dialog will be displayed, this dialog shows the select trustee and the constructed access token is displayed. To select the trustee click on the Select button and enter the details.
The Only display matching ACEs will limit the displayed ACEs that match the selected users access token, otherwise all ACE are displayed, included non-matching ACE (displayed with a gray icons).
The Display Effective Permissions Assignments will display the permissions assignments at the bottom section of the screen.
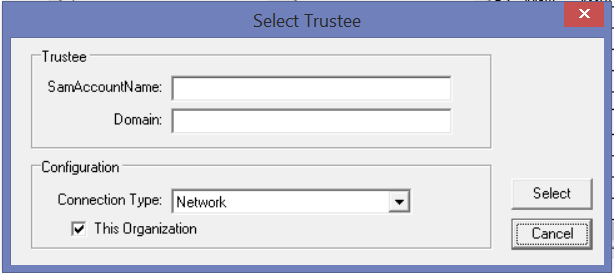
The Select Trustee dialog, allows you to specify the trustee and the connection method for the trustee, is used to construct the trustee's Access Token. Once the Trustee is selected, the Add and Remove buttons can be used to update the SIDs that are included in the constructed access token. This allow you to add groups or security principals to the token to see what impact this has on the trustee access rights.
With the Display Effective Permissions Assignments selected, the Effective Permissions panel is displayed. This shows the details of what permissions are assigned and which ACE is effective and the other permissions that didn't get assigned.
See Effective Permissions for more details.
Icons
![]() ACE assigned to an user, computer, etc.
ACE assigned to an user, computer, etc.
![]() ACE assigned to a group
ACE assigned to a group
![]() Unable to resolve the name of the SID assigned to the ACE
Unable to resolve the name of the SID assigned to the ACE
![]() The ACE is assigned to the trustee (Trustee Mode)
The ACE is assigned to the trustee (Trustee Mode)
![]() The ACE is assigned to the trustee (Trustee Mode)
The ACE is assigned to the trustee (Trustee Mode)
![]() The ACE is assigned to the Trustee, however, the permissions are not applied to this object (Trustee Mode)
The ACE is assigned to the Trustee, however, the permissions are not applied to this object (Trustee Mode)
![]() The ACE is assigned to the Trustee, however, the permissions are not applied to this object (Trustee Mode)
The ACE is assigned to the Trustee, however, the permissions are not applied to this object (Trustee Mode)
![]() The ACE is not applicable for the current Trustee (Trustee Mode)
The ACE is not applicable for the current Trustee (Trustee Mode)
![]() The ACE is not applicable for the current Trustee (Trustee Mode)
The ACE is not applicable for the current Trustee (Trustee Mode)
![]() The Trustee doesn't have permissions to the object (Trustee Mode)
The Trustee doesn't have permissions to the object (Trustee Mode)
![]() Additional ACE are assigned directly to the object
Additional ACE are assigned directly to the object
![]() Block Inheritance is enabled on the object
Block Inheritance is enabled on the object
![]() An error occurred reading the SD of the object
An error occurred reading the SD of the object
![]() Error reading or converting SD of the object
Error reading or converting SD of the object