This is in response to a query raised on ActiveDir.org maillist about how to check if a user has actually changed their password and not just toggled the pwdlastset attribute to make it look like they have changed their password. When a user changes their password a number of attributes are updated as a result of the password change, these include dbcspwd, lmpwdhistory, ntpwdhistory, pwdlastset, supplementalcredentials, and unicodepwd. To be able to determine if the password has actually been changed, we have to look at the meta data for the object and check the last change date of the unicodepwd attribute, which contains the hash of the user’s password.
NetTools provides a couple of ways to view the meta data of an object, via Meta data dialog, running an LDAP query, or in this use case the Last Logon, will display all the details required.
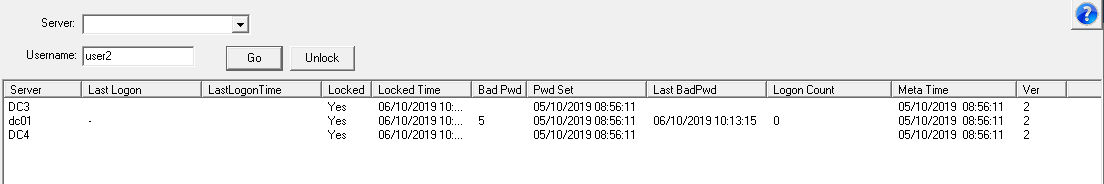
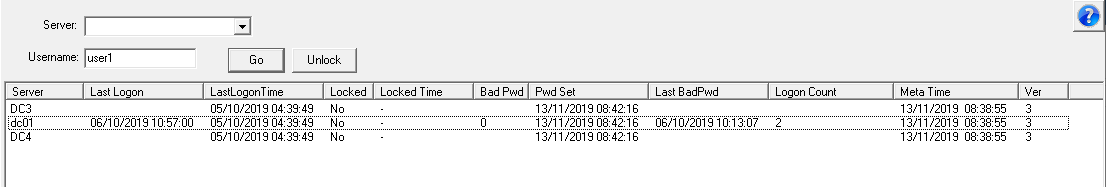
For a single user the Last Logon option will display both the pwdlastset and change date for the unicodepwd in the meta time column. This screenshot shows the results of a normal account password change, both the pwdlastset and meta time are the same.
For this user the pwdlastset has been toggled, and it shows that the pwdlastset and meta data times don't match
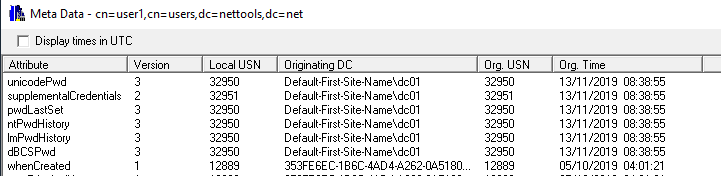
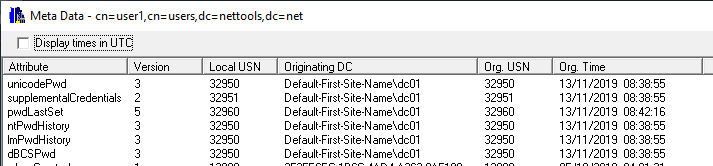
You can view the meta data on an object via the Meta Data Dialog, this option is provided throughout NetTools as a context menu option called Meta Data. The easiest place to demonstrate this on the User Search option, search the account in question and then right click on the user and select Meta Data from the right click context menu.
This shows an account that has had it's password changed.
This shows that the pwdlastset has changed but the other attributes have not changed, which is caused by the pwdlastset being toggled.
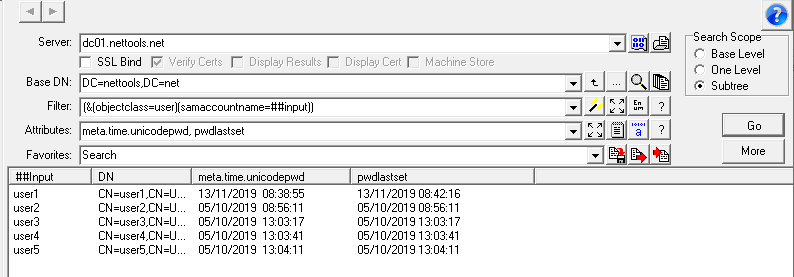
The above options are for single accounts, but it is also possible in to check multiple accounts at once. The LDAP Search option includes an option to return meta data as if it's an attribute of the object. This is done using the meta option in the attributes field. We can use an Input Mode of the LDAP Search to provide a list of the samaccountnames to check.
In this example we are checking the details of the five user accounts, and it shows that user1 meta data doesn't match the pwdlastset date and time.
Here is the favorite for the above query, see Favorites on how to import
[PwdLastSet Meta Data] Options=880030209675869 Server= BaseDN=##default Filter=(&(objectclass=user)(samaccountname=##input)) Attributes=meta.time.unicodepwd, pwdlastset DisplayFilter= Filename= Sort= Authentication=1158 Separator=,
With the introduction of v1.27, there is new query option that can be used to simplify this task. In v1.27 the conditional attributes have been extended to support meta data queries. This means we can do the checking in the query itself without any additional post query work.
[PwdLastSet Meta Data] Options=880030209675869 Server= BaseDN=##default Filter=(&(objectclass=user)(samaccountname=##input)) Attributes=samaccountname, Pwd_Change;{if:meta.time.unicodepwd;date!=pwdlastset:"Invalid":"Valid"} DisplayFilter= Filename= Sort= Authentication=1158 Separator=,
Related Articles
User Search
LDAP Search
LDAP Search Input Mode
Meta Data Dialog
Troubleshoot account lockouts
Favorites